Securing your websites with an SSL certificate is now a must for all website admins, else the web browsers will mark the website as unsafe to visit, causing the loss of website traffic. But SSL certificate is not cheap, but there is a way around to get an SSL certificate for free with the only downside that we need to renew SSL cert every 90 days but that process can also be automated. In this tutorial, we will discuss how we can configure an SSL on Nginx with Let’s encrypt.
We have already discussed in our previous tutorial, how we can configure SSL cert with Let’s certificate on Apache Web Server, so if you are using Apache you can check that tutorial. Now let’s start with the process to configure SSL on Nginx with Let’s Encrypt.
Recommended Read: Simple way to configure Nginx Reverse Proxy
Here we will discuss the method for Ubuntu & CentOS/RHEL using a let’s encrypt tool called 'certbot'. So let’s start with Pre-requisites,
Also Read: Analyzing APACHE logs in CLI (& GUI) using GoAccess
Pre-Requisites
- We will need a registered Domain address,
- We will need a CentOS/RHEL or Ubuntu server with Ngnix installed. Installation steps are mentioned below,
Ubuntu
Nginx is available with default Ubuntu Repositories. So simply install it using the following command,
$ sudo apt-get update && sudo apt-get install nginx
CentOS/RHEL
We need to add some repos for installing nginx on CentOS & we have created a detailed article here for Nginx installation on CentOS/RHEL.
Now start the services & enable it for boot,
# systemctl start nginx
# systemctl enable nginx
Once it's installed, we can move to the next part i.e. installing let's encrypt & issuing of SSL certificate on nginx with let's encrypt for the website.
Let's Encrypt on Ubuntu
Firstly we need to install Certbot on the Ubuntu system, but it's not available with default Ubuntu repositories. Install the Ubuntu repos with the following command,
$ sudo apt-get install software-properties-common
$ sudo add-apt-repository universe
$ sudo add-apt-repository ppa:certbot/certbot
$ sudo apt-get update
Now to install the Certbot, execute the following command from the terminal,
$ sudo apt-get install python-certbot-nginx
Now, we will issue a new SSL certificate using certbot command. Use the following command as reference,
$ sudo certbot --nginx -d linuxtechlab.com -d www.linuxtechlab.com
Here linuxtechlab.com is the name of the website for which the certificate will be issued, replace this with the name of your website. If this is the first time you are using Certbot, you will be asked to enter an Email address & also to agree to the User Agreement,
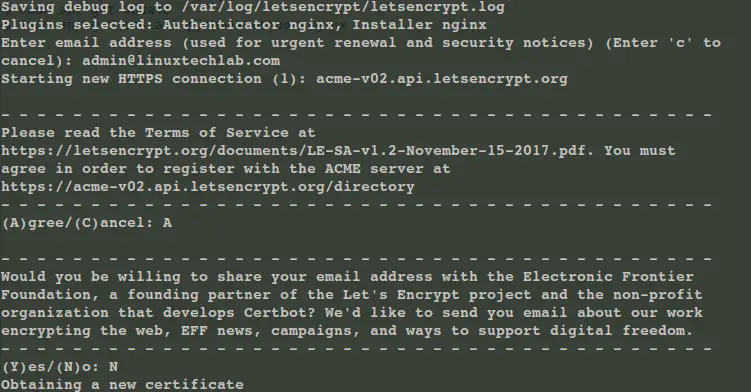
Now certbot will then check with the let’s encrypt server to verify that you are the web admin of the domain that you are trying to get an SSL for (usually you need to place two files with random text provided by let’s encrypt at location http://domain-name/.well-known/acme-challenge. more details on that HERE).
Once site ownership has been confirmed, we will be asked to configure redirect settings for Nginx, you can choose 1 (No-Redirect) or 2 (Redirect). If you choose 1, then you will have to configure redirect yourselves in Nginx configuration afterward, with option 2, the configuration will be updated & Nginx will be reloaded to implement the new changes made.
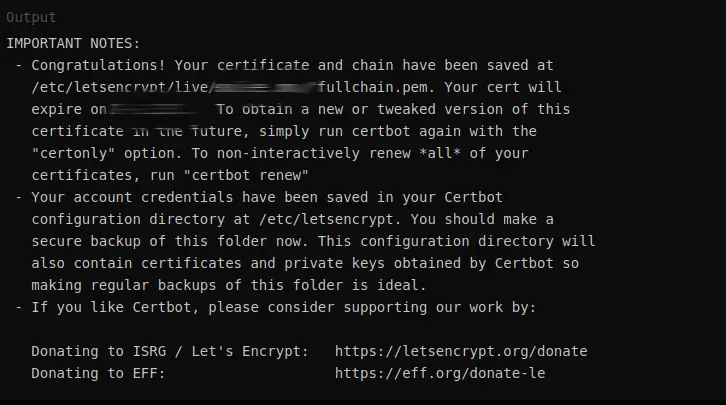
Our cert is now installed & new configurations also have been loaded. As mentioned above, we need to renew the cert every 90 days, for that, we can create a new cronjob, mentioned at the end of this tutorial.
Now let’s discuss the SSL issue procedure for CentOS & RHEL,
Let's Encrypt on CentOS/RHEL
To install Certbot on CentOS, we will need to first install EPEL repositories first on our system. Install EPEL using the following command on your system,
RHEL/CentOS 8
$ sudo dnf install https://dl.fedoraproject.org/pub/epel/epel-release-latest-8.noarch.rpm
RHEL/CentOS 7
# rpm -Uvh https://dl.fedoraproject.org/pub/epel/7/x86_64/Packages/e/epel-release-7-11.noarch.rpm
RHEL/CentOS 6 (64 Bit)
# rpm -Uvh http://download.fedoraproject.org/pub/epel/6/x86_64/epel-release-6-8.noarch.rpm
RHEL/CentOS 6 (32 Bit)
# rpm -Uvh http://dl.fedoraproject.org/pub/epel/6/i386/epel-release-6-8.noarch.rpm
Now we to install certbot use the following command,
# yum install certbot-nginx
Once the certbot has been installed, we can then issue the SSL certificate with the same command as mentioned above,
# certbot --nginx -d linuxtechlab.com -d www.linuxtechlab.com
Now the process will same as has been mentioned above for Ubuntu. Now after the cert has been installed, we need to make sure that the certificate is renewed before 90 days.
Automatic Certificate Renewal
Following cron job will take care of the automatic certificate renewal,
# crontab -e
05 01 30 * * /usr/bin/certbot renew --quiet
this job will renew the certificate every 30 days at 1:05 AM. We can also run the following command to dry-run or test the renewal of the certificate,
# certbot renew --dry-run
This completes our tutorial on how to configure SSL on Nginx with Let’s encrypt. However, if you wish to go with paid SSL option then, you can go with RapidSSL, Comodo, etc brands whose SSL certificate carries the highest server compatibility, for example, rapidssl wildcard certificate that can secure unlimited subdomains under a single main domain. Such certificates will not cost you more
Are you sure that you want to try and renew the certificate every day!?
Surely once a month is more than enough
You are right but this also works, but surely 30 days will also work fine.